New Progress ShareFile Bugs Let Attackers Take Over Servers Without Logging In

A dangerous attack chain in Progress ShareFile that can allow attackers to take over exposed on-premises servers without first logging in. The issues affect customer-managed ShareFile Storage Zones Controller 5.x deployments, and Progress says customers should upgrade to version 5.12.4 or move to any 6.x release, which is not impacted. According to Progress and WatchTower, […]
14,000+ F5 BIG-IP APM Devices Exposed Online Amid Active RCE Vulnerability Exploits

A critical security flaw in F5’s BIG-IP Access Policy Manager (APM) is currently under active exploitation, leaving thousands of enterprise networks at risk. The vulnerability, officially tracked as CVE-2025-53521, has sparked urgent warnings across the cybersecurity community after its impact was upgraded from a standard Denial-of-Service (DoS) to a severe Remote Code Execution (RCE) flaw. […]
Malicious Chrome Extension ChatGPT Ad Blocker Steals ChatGPT Conversations
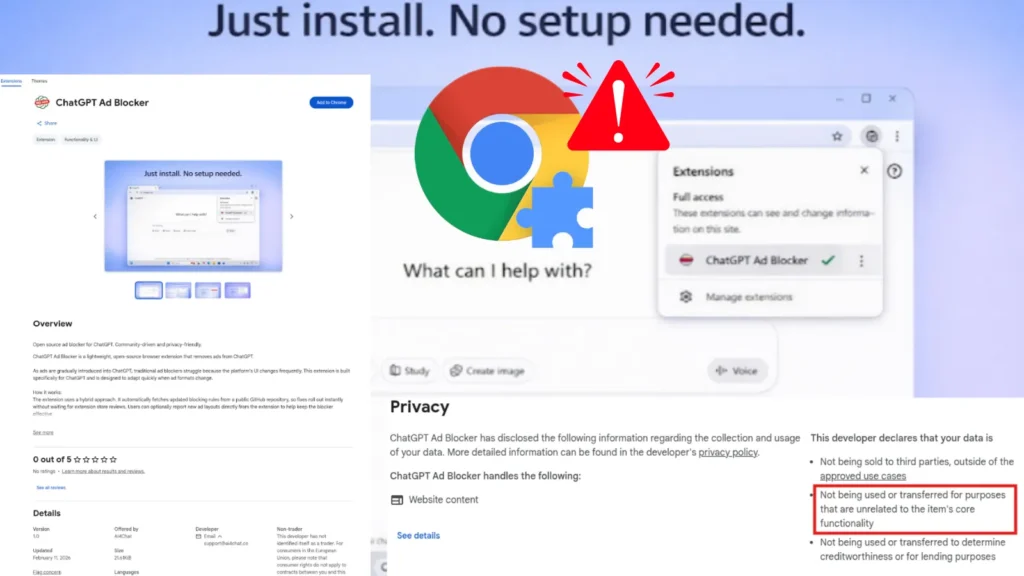
As OpenAI introduces advertisements to its free tier, cybercriminals are seizing the opportunity to trick users with fake utility tools. Security researchers have discovered a malicious Google Chrome extension named “ChatGPT Ad Blocker.” While it claims to hide unwanted ads, its true purpose is to steal private user conversations and send them to a hidden […]
Adobe Breach Threat Actor Allegedly Claims Leak of 13 Million Support Tickets and Employee Records

A threat actor identified as “Mr. Raccoon” has allegedly breached Adobe, claiming to have exfiltrated a massive trove of sensitive data, including 13 million support tickets containing personal information, 15,000 employee records, all HackerOne bug bounty submissions, and a range of internal documents, according to a report published by International Cyber Digest. According to details […]
Cisco Smart Software Manager Vulnerability Let Attackers Execute Arbitrary Commands

Cisco has issued an urgent security warning regarding a critical vulnerability in its Smart Software Manager On-Prem (SSM On-Prem) platform. Enterprise organizations widely use this tool to manage their Cisco software licenses locally. Tracked as CVE-2026-20160, the flaw carries a near-perfect CVSS severity score of 9.8 out of 10. If exploited, it allows an unauthenticated, […]
Vim Modeline Bypass Vulnerability Let Attackers Execute Arbitrary OS Commands

A newly discovered high-severity vulnerability in the popular Vim text editor exposes users to arbitrary command execution on the operating system. Tracked as CVE-2026-34982, the flaw relies on a modeline sandbox bypass that triggers when a victim opens a specially crafted file. Security researchers “dfwjj x” and Avishay Matayev identified a vulnerability chain that affects […]
Hackers Push CrystalX Malware-as-a-Service Through Telegram With Stealer and RAT Features

A new and dangerous piece of malware has surfaced and is being marketed openly to cybercriminals through private Telegram channels. Named CrystalX, this Malware-as-a-Service (MaaS) platform combines a remote access trojan (RAT), credential stealer, keylogger, clipboard hijacker, spyware, and an unusual set of prankware tools into one capable package. Discovered in March 2026, the malware […]
Hackers Weaponize Legitimate Windows Tools to Disable Antivirus Before Ransomware Attacks

Ransomware attacks have gone far beyond simple malicious code. Today, attackers operate with the precision of a well-planned business, using trusted Windows tools to quietly tear down defenses before ransomware even enters the picture. This shift has made modern ransomware campaigns harder to detect and significantly more damaging. The tools at the center of this […]
Google Unveils Ransomware Detection and File Restoration for Google Drive
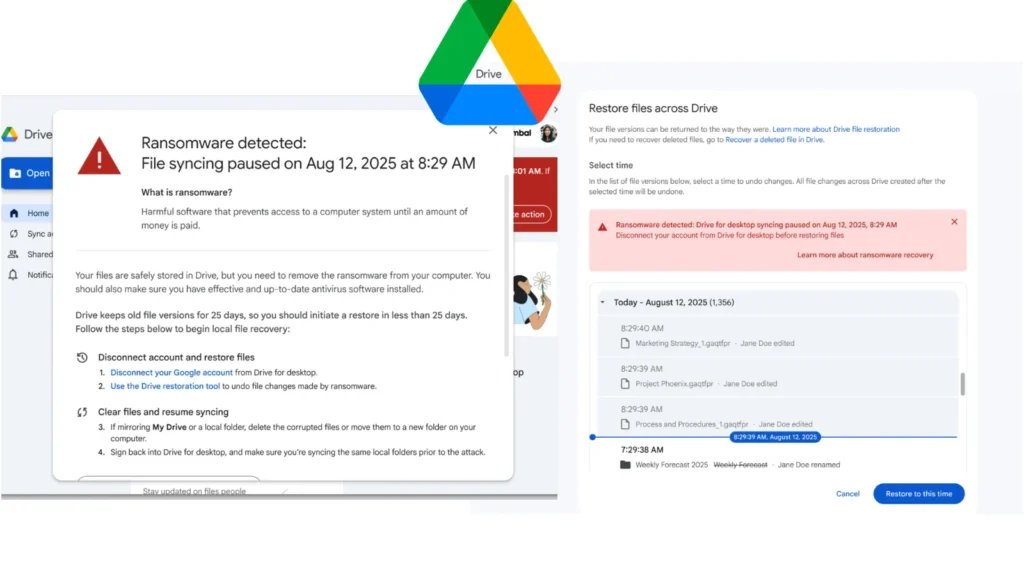
Google has officially moved its ransomware detection and file restoration features for Google Drive into General Availability. Originally launched in beta in September 2025, the updated security controls offer organizations enhanced defenses against malware attacks targeting local machines and cloud synchronization. The updated artificial intelligence model driving this release features significant performance improvements. The system […]
Anthropics Claude Code Source Code Reportedly Leaked Via Their npm Registry
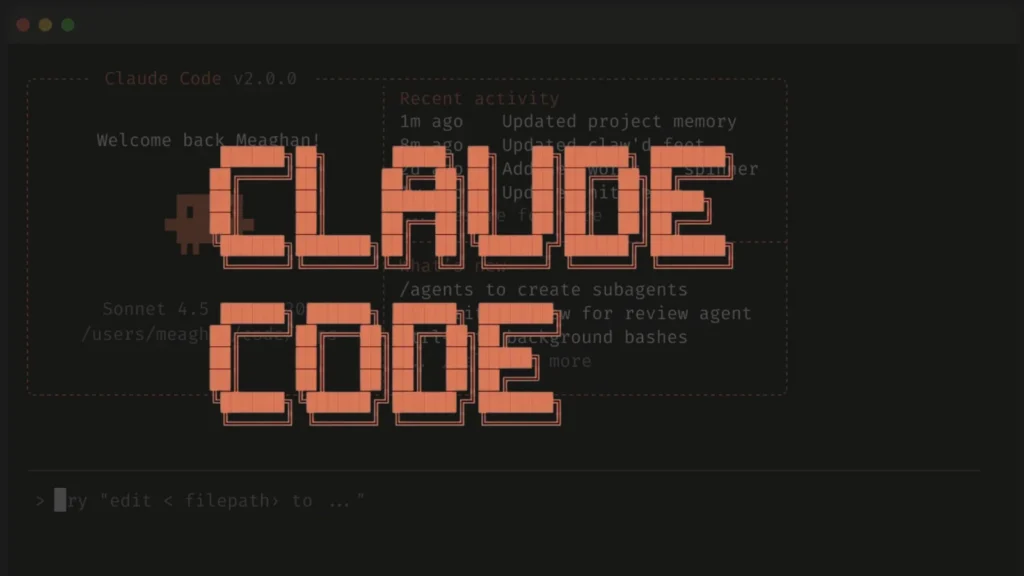
Anthropic’s proprietary Claude Code CLI tool has had its full TypeScript source code inadvertently exposed through a misconfigured npm package, after a security researcher discovered a leaked .map file referencing the unobfuscated codebase stored on Anthropic’s own cloud infrastructure. On March 31, 2026, researcher Chaofan Shou made the disclosure public, posting: “Claude code source code […]
