Google Unveils Ransomware Detection and File Restoration for Google Drive
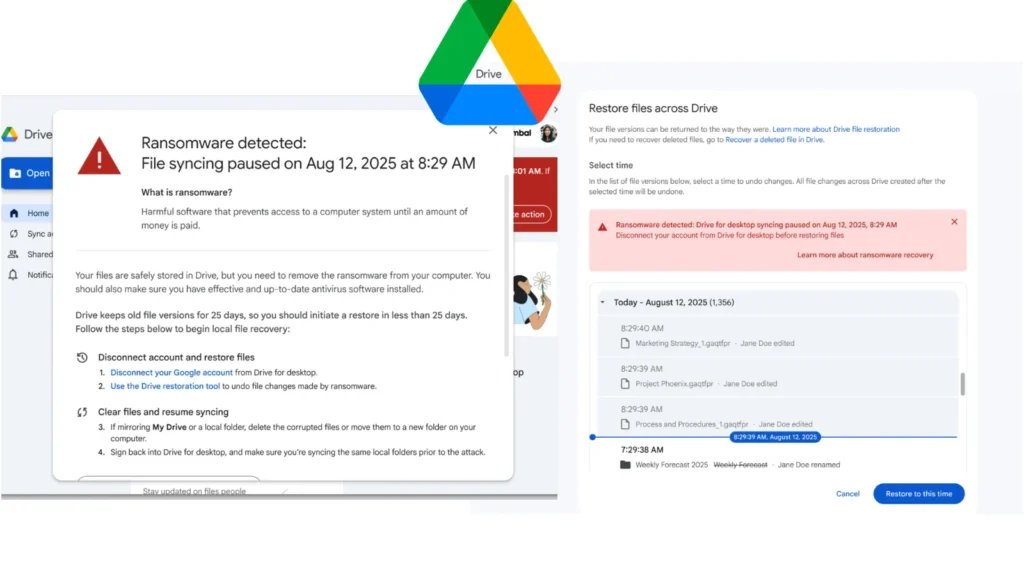
Google has officially moved its ransomware detection and file restoration features for Google Drive into General Availability. Originally launched in beta in September 2025, the updated security controls offer organizations enhanced defenses against malware attacks targeting local machines and cloud synchronization. The updated artificial intelligence model driving this release features significant performance improvements. The system […]
Anthropics Claude Code Source Code Reportedly Leaked Via Their npm Registry
Anthropic’s proprietary Claude Code CLI tool has had its full TypeScript source code inadvertently exposed through a misconfigured npm package, after a security researcher discovered a leaked .map file referencing the unobfuscated codebase stored on Anthropic’s own cloud infrastructure. On March 31, 2026, researcher Chaofan Shou made the disclosure public, posting: “Claude code source code […]
Axios NPM Packages Compromised to Inject Malicious Codes in an Active Supply Chain Attack
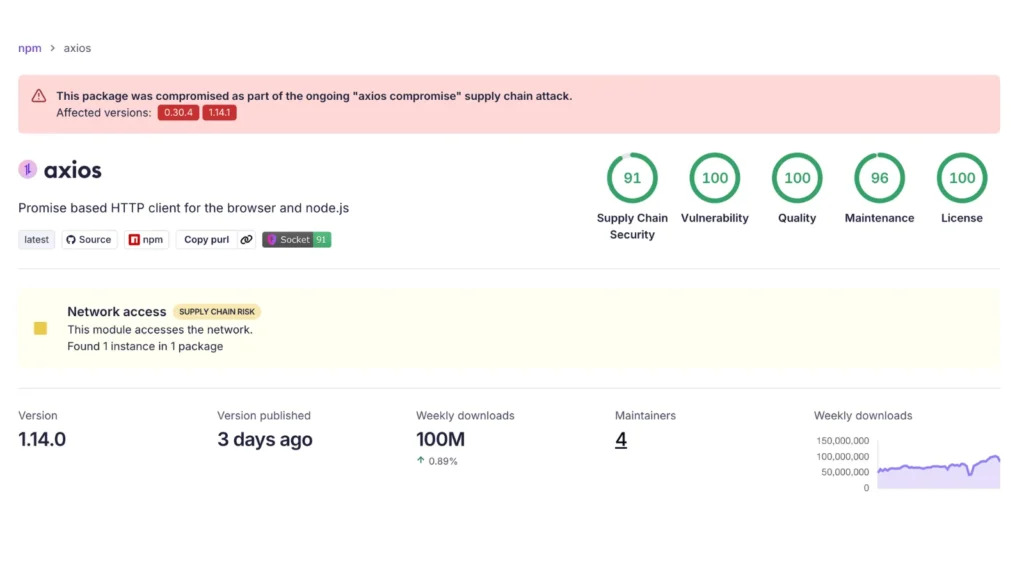
A sophisticated supply chain attack has targeted Axios, one of the most heavily adopted HTTP clients within the JavaScript ecosystem, by introducing a malicious transitive dependency into the official npm registry. Serving as a critical component across frontend frameworks, backend microservices, and enterprise applications, Axios records approximately 83 million weekly downloads on npm. The compromise […]
12 Best AWS Monitoring Tools in 2026
Best AWS Monitoring Tools Amazon Web Services (AWS) is a cloud computing platform for businesses of all sizes and types. AWS’s architecture is robust and scalable, but dependability, performance, and security must be monitored. These aims guide AWS’s monitoring tools and services, which help you understand your cloud infrastructure and applications, analyze data, identify outliers, […]
Critical Grafana Vulnerabilities Let Attackers Achieve Remote Code Execution

Urgent security updates for Grafana version 12.4.2 address two critical vulnerabilities that could allow attackers to achieve full remote code execution (RCE) and execute denial-of-service (DoS) attacks. System administrators utilizing Grafana for data visualization are strongly advised to apply these backported patches immediately to prevent potential system compromise. The most severe vulnerability, tracked as CVE-2026-27876, […]
10 Best Spam Filter Tools 2026
Spam Filter Tools Spam filter tools use advanced algorithms and machine learning techniques to detect and block unwanted email messages. They analyze email content, sender reputation, and patterns to effectively identify and filter out spam, ensuring inboxes remain clutter-free. These tools offer customizable filtering rules, allowing users to set specific criteria for identifying spam. This […]
Microsoft Issues Critical WinRE and Setup Updates Ahead of 2026 Secure Boot Certificate Expiration

Microsoft has rolled out two new dynamic updates, KB5081494 and KB5083482, designed for Windows 11 versions 24H2 and 25H2. Released on March 26, 2026, these patches deliver essential enhancements to setup binaries and the Windows Recovery Environment. Accompanying these technical releases is a critical advisory regarding the impending expiration of Windows Secure Boot certificates, urging […]
Hackers Probe Citrix NetScaler Instances Ahead of Likely CVE-2026-3055 Exploitation

Cybersecurity researchers are sounding the alarm over imminent in-the-wild exploitation of a recently disclosed critical vulnerability in Citrix NetScaler ADC and Gateway appliances. Threat intelligence firm watchTowr and Defused Cyber have detected active reconnaissance campaigns specifically targeting CVE-2026-3055, a high-severity memory overread flaw that could allow unauthenticated attackers to extract sensitive data. Organizations relying on […]
Cybersecurity Companies Stocks Fall as Anthropic Tests Powerful New Model

Cybersecurity stocks declined sharply on Friday following revelations that Anthropic has begun testing “Mythos,” an extraordinarily powerful new AI model with advanced vulnerability-discovery capabilities. Anthropic is actively trialing a new tier of artificial intelligence models codenamed “Capybara,” with the flagship model operating under the moniker “Mythos”. Internal documents indicate that Mythos significantly outperforms the company’s […]
CISA Warns of F5 BIG-IP Vulnerability Actively Exploited in Attacks

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a newly disclosed vulnerability affecting F5 BIG-IP systems to its Known Exploited Vulnerabilities (KEV) catalog, warning that the flaw is being actively leveraged in real-world attacks. The vulnerability, tracked as CVE-2025-53521, was officially listed on March 27, 2026, with a remediation deadline of March 30, […]
